
Pretty sneaky, Microsoft. While some vendors were scrambling to release updates to fix the KRACK Attack vulnerability released today, Microsoft, quietly snuck the fix into last week's Patch Tuesday.
While Windows users were dutifully installing October 10th's Patch Tuesday security updates, little did they know they were also installing a fix for the KRACK vulnerability that was not publicly disclosed until today. This fix was installed via a cumulative update that included over 25 other updates, but didn't provide any useful info until you visited the associated knowledge basic article.
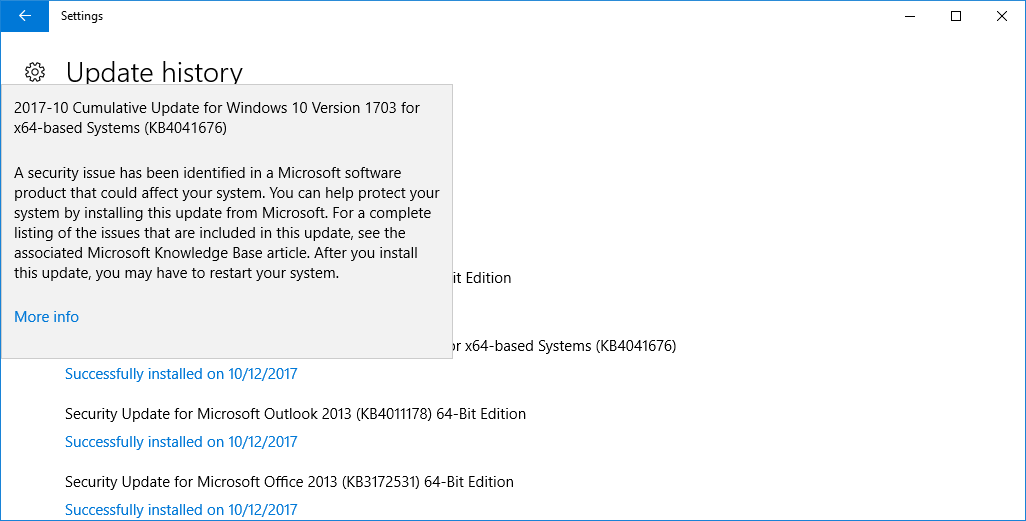
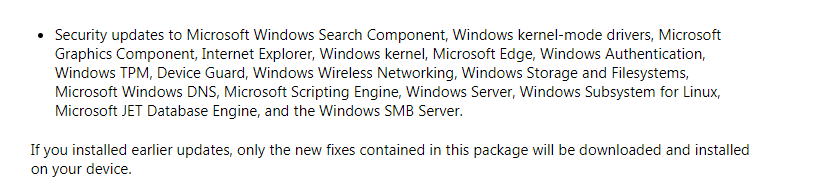
Even if you were bored enough to actually click on the More info button, you would have had to be REALLY bored to even spot a reference to a vague mention of a wireless security update in the last bullet item of the knowledge base article.
A Microsoft spokesperson told BleepingComputer that "Microsoft released security updates on October 10th and customers who have Windows Update enabled and applied the security updates, are protected automatically. We updated to protect customers as soon as possible, but as a responsible industry partner, we withheld disclosure until other vendors could develop and release updates.”
While, I am not typically a fan of sneaky updates, I understand why it was necessary to fix the vulnerability while keeping information about it secret until it was officially disclosed.
Did Microsoft do the right thing quietly patching the update or is full disclosure the only way to go? I will let you decide.
As for the rest of the vendors releasing updates, BleepingComputer has been compiling a list of advisories and updates here: List of Firmware & Driver Updates for KRACK WPA2 Vulnerability.


Comments
Occasional - 6 years ago
Than you LA - both for the post and the question.
What I'd like to see is a policy, with specific guidelines for vendors, as to how they should handle discovered vulnerabilities which extend beyond their products.
MS probably did the best-for-most, after making sure their customers were covered. Although I'd rather not leave these decisions up to any one company.
From a liability standpoint, I'd think companies would prefer to have the legal cover of being able to say "we complied with..." rather than someone claiming they suffered because of whatever choice they made.
LConstantin - 6 years ago
The researcher who found the flaws doesn't appear to think silent patches are a good idea. OpenBSD did the same thing and here is what he said in the FAQ on the KRACK website:
"Why did OpenBSD silently release a patch before the embargo?
OpenBSD was notified of the vulnerability on 15 July 2017, before CERT/CC was involved in the coordination. Quite quickly, Theo de Raadt replied and critiqued the tentative disclosure deadline: “In the open source world, if a person writes a diff and has to sit on it for a month, that is very discouraging”. Note that I wrote and included a suggested diff for OpenBSD already, and that at the time the tentative disclosure deadline was around the end of August. As a compromise, I allowed them to silently patch the vulnerability. In hindsight this was a bad decision, since others might rediscover the vulnerability by inspecting their silent patch. To avoid this problem in the future, OpenBSD will now receive vulnerability notifications closer to the end of an embargo."
Occasional - 6 years ago
Interesting, and informed, perspective.
Hadn't considered mining patches to discover vulnerabilities in my comment. The scope of a vendor's concern would seem to be a factor - easier to bury the target vulnerability for a patch when you have so many other updates going out in the same bundle (and "in phase"), as with MS.
The quote you posted also suggests timing is very important. MS patch went out a bit less than a week before public disclosure; so not much time to mine and exploit.
The quote also raises questions about researchers deciding (or negotiating), the who, what, when and how of disclosure. What this one decided (both initially and on reflection), seems reasonable (to me, given my limited knowledge). What about the next time, and the next guy?
Occasional - 6 years ago
From Wi-Fi.org: "...There is no evidence that the vulnerability has been exploited maliciously..." (10/16).
Did the collective we dodge a bullet with this one, or will knowing depend on 1) How long it takes to get patches available, 2) How long it will be before every host and client device is updated?
Every IT department worth its salt is already on the case for their organization; but will their efforts hinge on what John and Jane Q Public (and all the organizations that work without an IT net), do or don't do?
Getting back to the question of quiet patching - would it help to push security notices, without details or patches, shortly before public release? Should the public release date be included - so IT departments won't get caught short?
Maybe something like: "A significant security issue has arisen concerning all Wi-Fi devices. Your Wi-Fi device maker's website will be the best source for news and software updates specific to your device."